Why Asset Inventory Is the Foundation of Industrial Cybersecurity
You Cannot Protect What You Cannot See
Ask any plant manager how many devices are on their OT network. In most cases, the honest answer is: "We're not entirely sure."
This is not a failure of competence — it is the natural result of how industrial environments evolve. Equipment is installed during construction, replaced during shutdowns, added by vendors during upgrades, and connected by integrators during expansions. Over years of operation, the gap between what is documented and what actually exists grows wider.
And yet, every cybersecurity decision depends on knowing what is there.
The Problem with Manual Inventories
Many organisations attempt to maintain asset registers through manual surveys — spreadsheets updated after commissioning, or periodic audits conducted by external consultants. These efforts are valuable, but they share a common limitation: they become outdated the moment they are completed.
A new device appears on the network between audits. A contractor replaces a switch and does not update the register. A vendor connects a laptop for diagnostics and leaves it on the network. A PLC firmware version changes during remote maintenance. None of these events are captured until the next survey — if they are captured at all.
In the meantime, the organisation is making security decisions based on an incomplete picture.
Why It Matters for OT Specifically
In IT environments, asset management is well established. Endpoint management platforms, Active Directory, and cloud dashboards provide continuous visibility over servers, workstations, and services.
OT environments are fundamentally different. Industrial devices — PLCs, RTUs, drives, relays, sensors — do not register themselves in a directory. Many do not support agents or management protocols. They communicate over industrial protocols that are invisible to IT asset management tools.
The result is that OT networks often contain devices that nobody knows about, running software that nobody has audited, communicating in ways that nobody is monitoring.
This is not a theoretical risk. It is the everyday reality of most industrial facilities.
What a Continuously Maintained Inventory Provides
A real asset inventory — one that is discovered automatically and maintained continuously — changes the operational picture fundamentally:
Visibility into every device — not just the ones that were documented during commissioning, but every device that is actually communicating on the network right now. This includes PLCs, HMIs, switches, cameras, laptops, and anything else that has a network presence.
Software and firmware awareness — knowing not just that a PLC exists, but what firmware version it is running, what software is installed on each Windows endpoint, and whether any known vulnerabilities apply to the current inventory.
Change detection — understanding when something changes. A new device appears. A firmware version is different from yesterday. Software was installed on an HMI workstation overnight. These changes are detected in real time, not discovered months later during an audit.
Accountability — when a change is detected, the platform provides context: when it happened, what the previous state was, and what communications were associated with the change. This transforms asset management from a static register into a living operational record.
The Regulatory Dimension
Asset inventory is not just good practice — it is increasingly a regulatory requirement.
IEC 62443 requires organisations to identify and document all assets within their industrial automation and control systems. IACS Unified Requirements UR E26 mandates comprehensive asset inventories for vessels. National critical infrastructure frameworks across multiple jurisdictions require operators to maintain current records of their OT assets.
In each case, the requirement is clear: you must know what you have before you can demonstrate that you are protecting it.
A manually maintained spreadsheet may satisfy the letter of the requirement, but it cannot provide the confidence that comes from a continuously verified, automatically maintained inventory.
How First Watch Approaches Asset Inventory
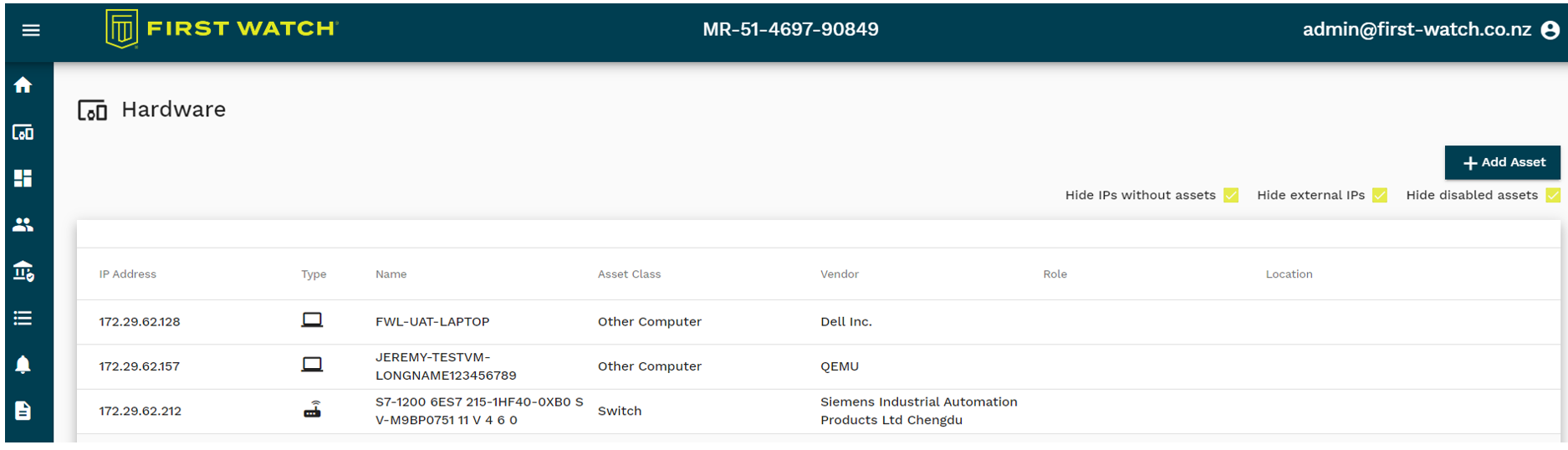
First Watch builds asset inventory as a natural by-product of its monitoring capabilities. PLC Guard observes network traffic and automatically identifies every device communicating on monitored networks — extracting vendor information, model details, firmware versions, and communication patterns without requiring agents or manual configuration.
ControlGuard agents on Windows-based endpoints provide detailed software inventories — every installed application, version, and installation date — along with automatic matching against known vulnerability databases.
Together, these capabilities provide a comprehensive, continuously updated picture of the entire OT environment. Not a snapshot from last quarter's audit, but the actual state of the network right now.
The Starting Point, Not the End Goal
Asset inventory is not the final destination of an OT cybersecurity programme — but it is the essential starting point. Without it, every other capability — monitoring, detection, enforcement, compliance reporting — is built on assumptions rather than facts.
When you know exactly what is on your network, who is communicating with what, and what software is running on each device, you can make informed decisions about what to protect and how. Without that knowledge, you are guessing.
And in industrial environments, guessing is not an option.