Can You Really See Everything on Your OT Network?
The Confidence Gap
Most plant managers and control engineers have a mental model of their OT network. They know which PLCs control which processes. They know where the HMIs are. They know which SCADA server talks to which controllers.
But that mental model was built over time — from commissioning documents, maintenance records, and accumulated experience. It reflects what was designed, not necessarily what exists today.
The question is simple: can you really see everything that is happening on your OT network right now?
For most organisations, the honest answer is no.
What Monitoring Actually Shows You
Deploying a monitoring solution on an OT network is a revealing experience. Almost without exception, the first thing operators discover is devices they did not know about.
A switch installed during a past upgrade that was never documented. A vendor laptop left connected after a maintenance visit. A legacy PLC that was supposed to be decommissioned but is still communicating. A wireless access point added by a contractor for convenience.
These are not hypothetical examples — they are findings that repeat across every industry, every site, every deployment.
Beyond unknown devices, monitoring reveals unexpected communication patterns. Systems talking to destinations they should not reach. Protocols being used in ways that were not part of the original design. Traffic crossing network boundaries that were assumed to be isolated.
The Layers of Visibility
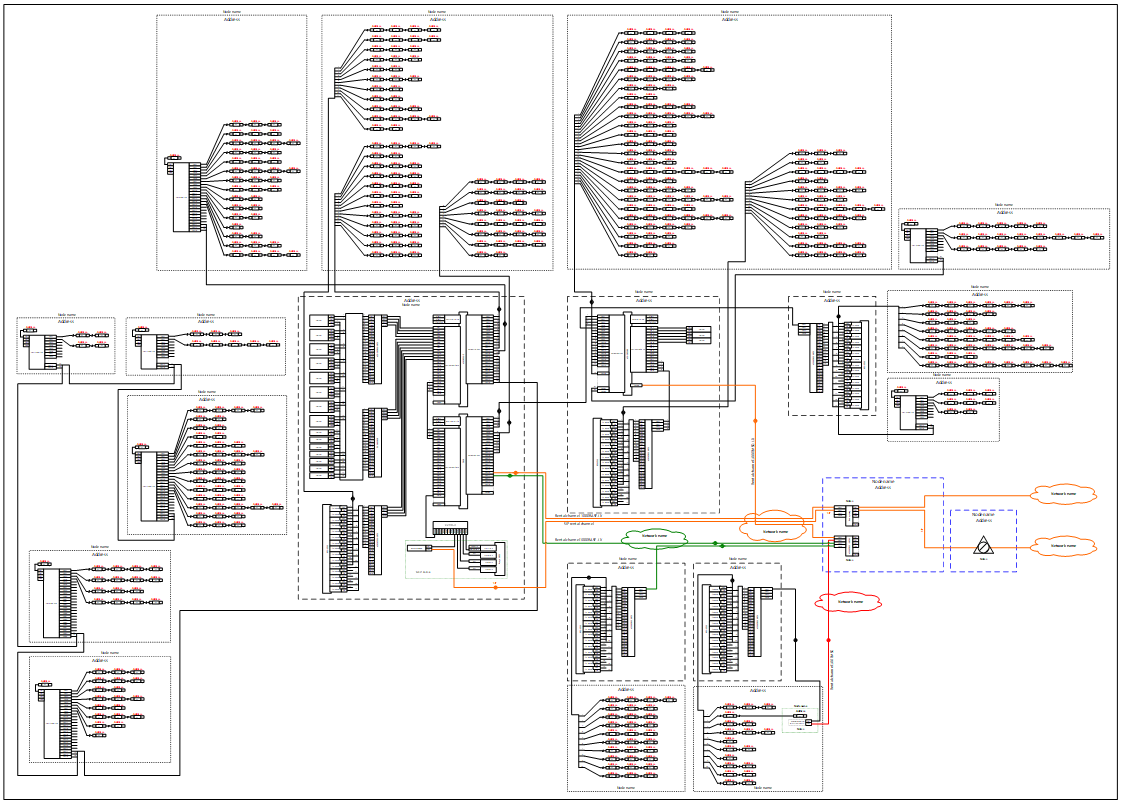
True visibility in an OT environment is not a single capability — it is built from multiple layers, each revealing something the others cannot.
Network-level visibility shows which devices are communicating, over which ports and protocols, and how frequently. This is the foundation — but it only tells you that traffic exists, not what it means.
Protocol-level visibility goes deeper. By inspecting the content of industrial protocols — Modbus, CIP, S7Comm, DNP3 — you can see the actual operations being performed: register reads, setpoint writes, firmware downloads, logic changes. This is where the operational meaning becomes visible.
Endpoint-level visibility reveals what is happening inside the Windows-based systems on the network — HMIs, historians, engineering workstations. Which software is installed, what processes are running, what USB devices are connected, what configuration changes have been made.
Change-level visibility tracks how the environment evolves over time. A new device appears. A firmware version changes. Software is installed or removed. A PLC programme is modified. Without this temporal dimension, you only see a snapshot — not the story.
What You Still Cannot See
Even with comprehensive monitoring, there are limits to pure observation.
Monitoring tells you what happened. It does not tell you whether it was supposed to happen. A firmware download to a PLC looks the same whether it was performed by an authorised engineer during a maintenance window or by an unknown party at 3am on a Sunday.
This is why visibility alone is not sufficient. It is the essential starting point — but the next step is enforcement: defining what is permitted and blocking everything else.
The Real Value of Seeing Everything
When an organisation achieves genuine visibility over its OT environment, something important changes. Conversations shift from assumptions to facts.
Instead of "I think we have about 50 devices on the network," it becomes "We have 73 devices, and three of them appeared in the last week."
Instead of "Our PLCs haven't been changed since commissioning," it becomes "PLC-7 firmware was updated on Tuesday at 14:32 by a remote session from the vendor's support centre."
Instead of "Our network is segmented," it becomes "Here are the 12 communication flows crossing the boundary between zones A and B, and four of them were not part of the original design."
This is the foundation on which every other cybersecurity capability is built. You cannot write a policy for assets you do not know about. You cannot detect anomalies without a baseline. You cannot enforce controls without understanding what normal looks like.
Getting Started
The path to genuine OT visibility does not require a massive infrastructure project. First Watch deploys PLC Guard on a SPAN port to passively observe network traffic — discovering assets, mapping communications, and identifying industrial protocol operations without touching production systems.
ControlGuard agents on Windows endpoints add the software and process layer. Together, they build a continuously maintained picture of the entire OT environment.
The first step is always the same: connect, observe, and find out what is really there. The results are almost always surprising — and that surprise is exactly why visibility matters.